System architecture
Get to know the architecture of the Authorization Control Plane (ACP) environment.
Logical architecture
In a distributed service provider environment, there are six participants that take part in the authentication and authorization process:
-
Authorization provider: Authorization Control Plane
-
The user or an application
-
Identity provider
-
API Gateway / Enforcement solution provider
-
MicroPerimeter™ Authorizer
-
APIs running on, for example, Docker or Kubernetes
The diagram below presents the logical architecture for the ACP of distributed authentication, authorization, and API enforcement services.
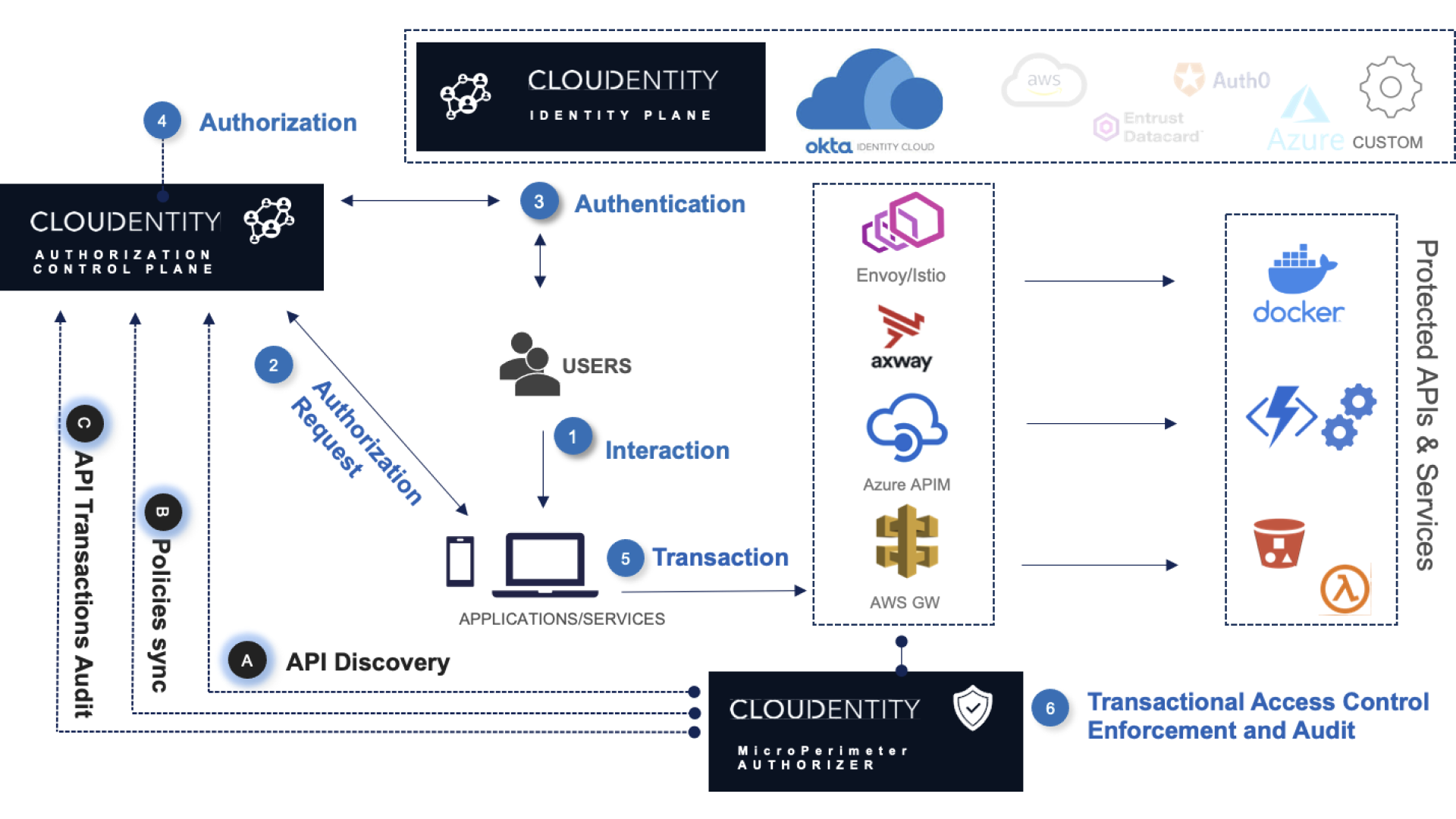
ACP, as a safeguard for your APIs and applications, steps into action when an OAuth/OIDC flow is initiated. It may be triggered by a user interacting with your application, or it can happen outside the context of a user in some of the OAuth flows (for example, the client credentials flow) in a machine-to-machine environment. If needed, ACP initiates user authentication via the configured identity provider. The client application communicates with ACP to get authorization and authenticates itself with ACP. After the client application is authenticated, the application requests resources (APIs) through the API calls. Those APIs are protected by the API Gateways or Enforcement solutions. The MicroPerimeter™ Authorizer participates in the process bringing the transactional access control enforcement and audit.