Configurable External Authorization for APIs
Configure external authorization for APIs using the Authorization Control Plane (ACP)
In a nutshell
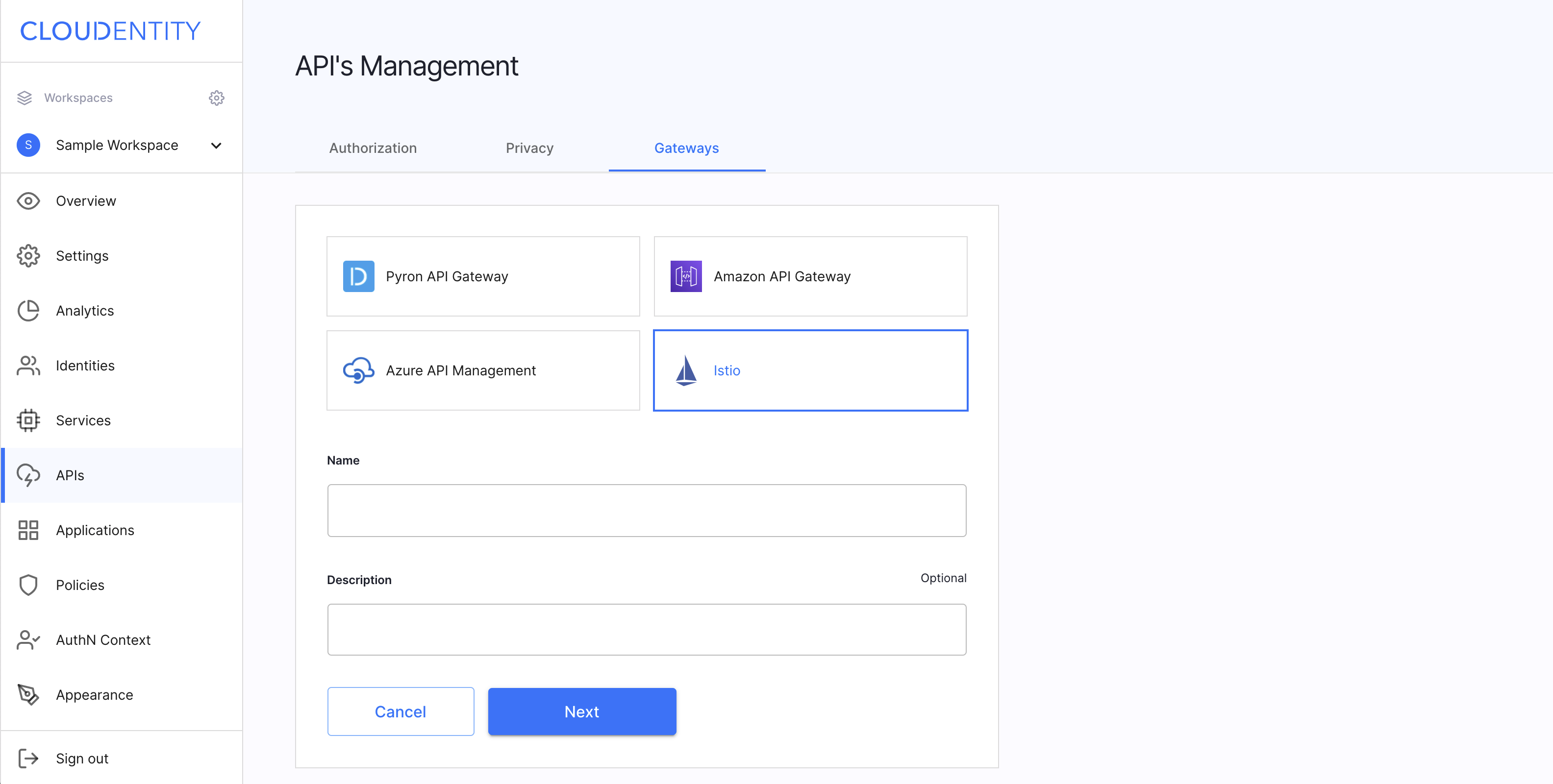
The Standalone Authorizer provides an external authorization service for API gateways and applications. Cloudentity provides a number of authorizers that are integrated with specific API Gateway products, such as Amazon’s AWS API Gateway, or the Istio service mesh.
The Standalone Authorizer is unique, because it is not specialized to any single product or technology, and is capable of serving in a variety of use-cases. This flexible option for external authorization, allows policy management for API access to be managed centrally, with benefits to visibility and auditability.
The Standalone Authorizer provides these key capabilities:
- Enables API definitions to be configured and updated in real time.
- Sychronizes access policy updates from the ACP.
- Enables inquiry against embedded policy decision engine to assess if specific operation is allowed.
External Authorization
Authorization is vast enough to be addressed by specialized products. Its requirements are in particular driven by frequently non-trivial real-life use cases and security requirements. To satisfy those requirements, authorization products need a broader context, and become part of a broader ecosystem. The Standalone Authorizer externalizes authorization decisioning so that those requirements can be satisfied by products built for that purpose. It delivers elements that authorization decisioning needs in distributed applications, such as authentication, enforcement points, and infrastructure to pass the context to the authorization engine.
Authorization Control Plane and microservice APIs
An effective authorization policy that controls resource access is usually distributed between an authorization server and a resource server. In a distributed application system, resource servers are composed of microservices that expose certain APIs for external consumption. It implies that an effective authorization policy is not limited to the edge gateway, but spans deeper into an individual microservice participating in the request handling and its API.
ACP provides comprehensive and easy-to-govern authorization for APIs. Policies at the authorization server level and those applicable at edge APIs, or microservice APIs, are managed centrally. ACP needs to know about all APIs to let easily assign authorization policies to each one of them, and to provide visibility and governance.
Below, you can find a screenshot of the ACP API Gateway Management page.
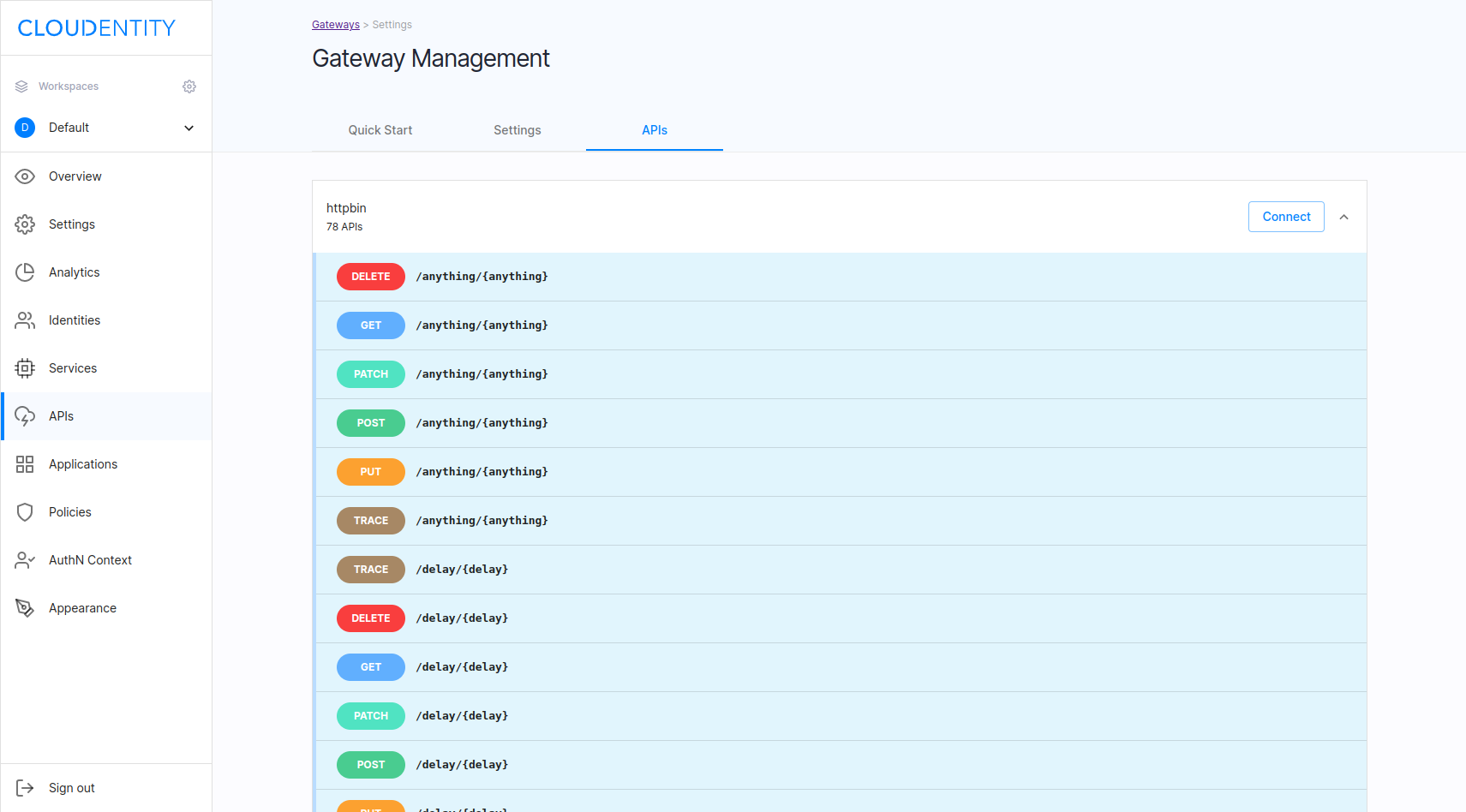
ACP provides authorization for microservice APIs and edge APIs maintaining unified developer experience. The Standalone Authorizer allows you to configure all APIs in ACP, regardless whether they are protected by an API gateway.
Dynamic Authorization
The Standalone Authorizer brings the advanced authorization capabilities offered by ACP to distributed applications, in a cloud-centric and technology-agnostic way. The most notable capabilities are the following:
- Distributed authorization with centralized management,
- ABAC, RBAC, Fine-grained authorization,
- Authorization policy governance,
- API authorization unification across diversified environments,
- WYSIWYG policy editor with ready to use building blocks, policy versioning, REGO based policies,
- Policy decisioning context (for example, user, security feed, request, threat analytics),
- Policy callouts to external APIs.
Unified authorization for distributed microservices
ACP is comprehensively focused on APIs authorization irrespective of what type of service exposes them and how it is deployed. Integration with the Standalone Authorizer does not impact availability of other integration patterns with microservices and services that are not part of the zero trust network.
APIs of services that are not a part of the zero trust network, can still take advantage of external authorization, by directly calling the policy decision point APIs that the Standalone Authorizer provides. It can be managed using a single ACP workspace or distributed among multiple workspaces and tenants if needed.
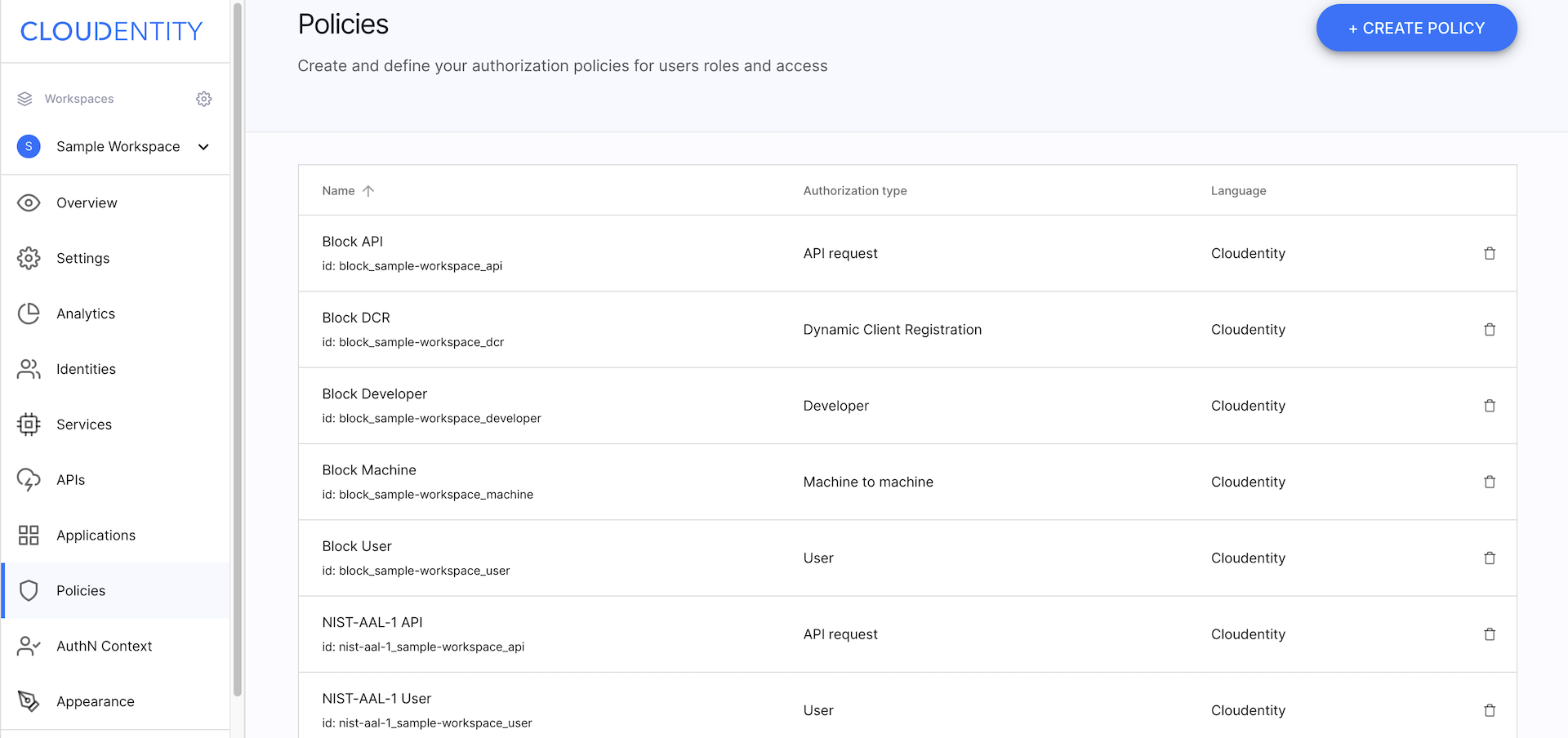
Authorization Servers
ACP provides comprehensive authorization for APIs. Each ACP workspace contains an authorization server instance. Each workspace has a collection of authorization polices and APIs exposed through the gateways that the workspace is connected to. Authorization policies can be assigned and enforced at the authorization server level and/or endpoint level. It is sole solution implementer’s decision whether Cloudentity is used for the first, the latter, or both.
When ACP is integrated with the Standalone Authorizer, it primarily does externalized policy decisioning at the endpoint level. Beyond this service-to-service authorization use case, it also covers authorization and authentication use cases related to the consumption of externally exposed APIs.
To do that, ACP is integrated as an authorization server/OpenID Connect Provider. Authorization server instances associated with each ACP workspace come with rich authorization capabilities and attribute mapping capabilities. It gives freedom in shaping subject attributes delivered to externally facing APIs.
Application of both integration patterns in conjunction is recommended to get the most value out of ACP in terms of access control and authorization governance. It is because, in such a setup, ACP allows to manage effective API authorization centrally and enforce it in a distributed fashion. Such API authorization includes also “preauthorization” happening at the authorization server level that may encompass user consent, transaction authorization, ABAC, RBAC, and others.
GitOps
ACP, and the Standalone Authorizer, are easily incorporated into GitOps workflows, making it an ideal tool for DevSecOpses. Authorization policies are stored in Git repositories, and when a policy is changed, ACP pulls the changes from the Git repository. This practice makes policies easy to version and use in DevSecOps pipelines. At the same time, policies are easy to audit and design using a visual editor. Similarly, API configurations can also be stored in Git, and changes to APIs can be applied via the Standalone Authorizer.