Acquiring authentication context from Lambda Authorizers
Instructions on how to use the INJECT_CONTEXT variable to enable the services to retrieve authentication context from ACP's access tokens.
About getting authentication context data
If ACP is set to provide opaque access tokens as a mean of authenticating client applications that make requests to services deployed behind the AWS API Gateway, it is impossible to retrieve any information on the user from the token itself. Because of that ACP’s Lambda Authorizer can inject authentication context to additional Lambda Functions that retrieve the context passed from the authorizer.
In a traditional setup of AWS API Gateway and ACP’s AWS Lambda Authorizer, request transformation, response transformation and status code setting is done in the API Gateway. If your API gateway integration is set to Lambda Function and uses Lambda Proxy integration, your Lambda Function receives the whole request (such as query parameters, request body, and variables) including the authentication context passed by the AWS Lambda Authorizer. Additionally, the response is sent from your custom Lambda Function.
Using Lambda functions instead of the traditional setup is easier to configure. Both the status code and the response messages are in your custom Lambda control. You can prototype rapidly as you do not need to set up your API Gateway. Additionally, you can retrieve the information on the users from the AWS Lambda Authorizer and use them according to your needs.
Below, you can find a simplified diagram of the Lambda Authorizer - API Gateway - Lambda Proxy integration.
When a client application makes a request to an API deployed behind the AWS API Gateway, the gateway invokes ACP AWS Lambda Authorizer that is responsible for policy decisioning and enforcing access control. After the authorizer responds to the gateway and injects authentication context to the response, the gateway proxies the request to the Lambda Function that is responsible for providing the request response and status codes.
Prerequisites
-
You have an AWS console account with all required permissions to manage your Lambda Functions and API gateways.
-
APIs are deployed behind your AWS API Gateway.
-
You had set up access control enforcement for your APIs deployed behind the AWS API Gateway and use ACP’s Lambda Authorizer as described in the Protecting APIs deployed behind the AWS API Gateway article.
Retrieve authentication context from Lambda Authorizer
-
In your AWS Management Console Lambda Authorizer’s settings, add the
AWS_INJECT_CONTEXTenvironment variable with value set totrue.AWS_INJECT_CONTEXT variable
If the
AWS_INJECT_CONTEXTvariable is set to true, it is possible to inject base64-encoded authentication context to the target service in order to, for example, provide the target service with information on logged in user.To learn how to configure your environment variables for your authorizer, see the Create a function section, step 7.
To learn about ACP AWS Lambda Authorizer configuration, see its configuration reference.
-
Prepare a Lambda Function that will serve as your Lambda Proxy integration.
Your custom Lambda Function should follow the guidelines present in the AWS Setting up Lambda custom integrations article. Adjust the event handler according to your needs. For example, you can provide your request responses and status codes.
Below, you can find a simple example of a
lambda_handlerthat responds with theHTTP 200status code and dumps a JSON response body. The body includes the base64-encoded authentication context that the Lambda Function receives from the Lambda Authorizer.import json def lambda_handler(event, context): print(json.dumps(event)) return {'statusCode': 200, 'body': json.dumps(event)} -
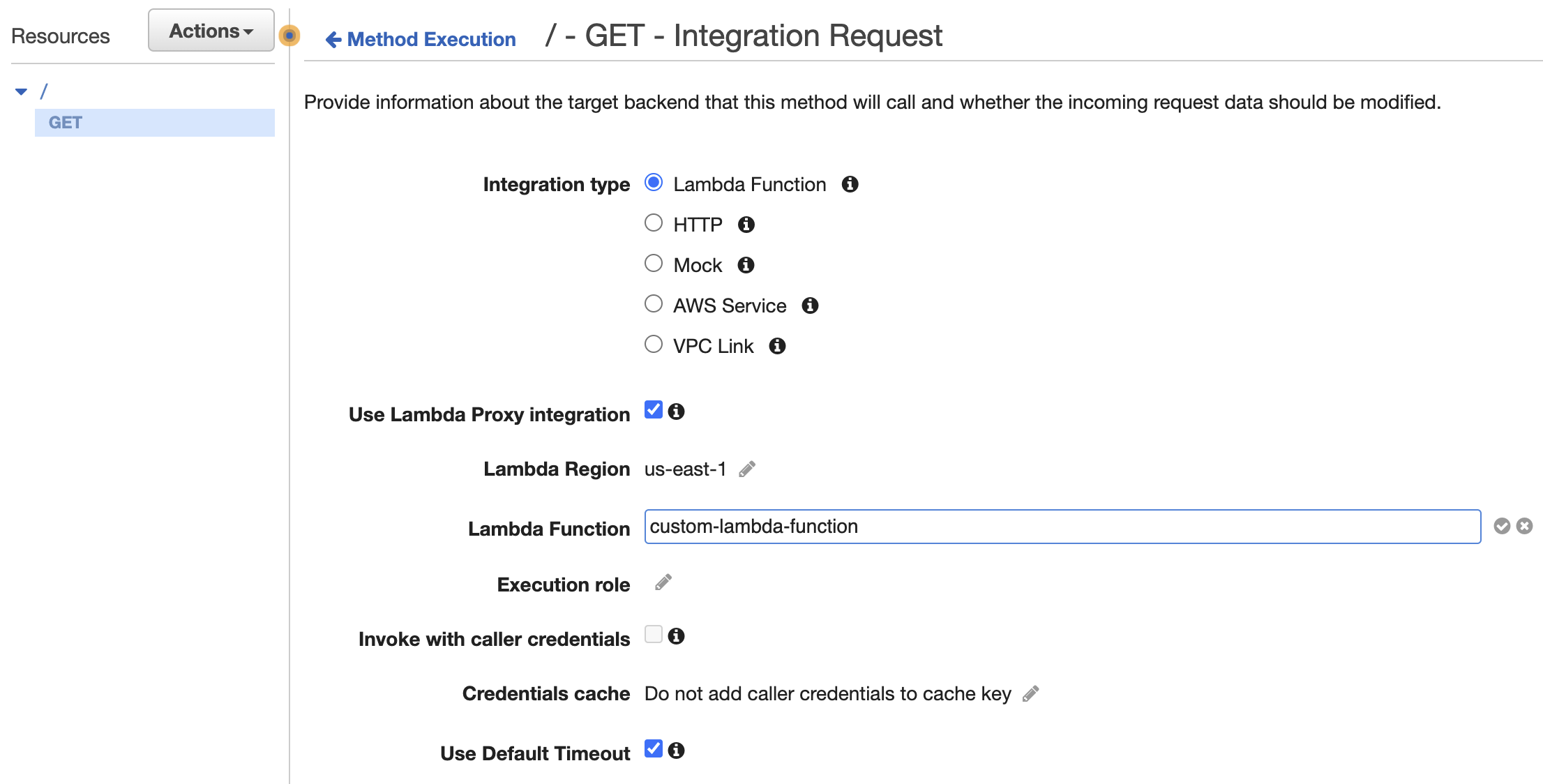
Go to your AWS API Gateway > Resources, choose a particular method and add an Integration Request.
-
Set the integration type to Lambda Function.
-
Enable the Use Lambda Proxy integration checkbox.
Lambda Proxy integration
The request to your APIs will be proxied to your Lambda Function that you created in the second step with the request details available in the
eventobject of your handler function. -
Provide the identifier of your custom Lambda Function that you created in the second step as the value for the Lambda Function input field.
-
-
Make a request to the API that you protect with the ACP AWS Lambda Authorizer and that you had applied with a custom Lambda Function integration.
If you used the custom lambda_handler Lambda Function provided in the second step, you can see
that the request response contains the following response body in the JSON format:
Under the requestContext and authorizer objects, you can find the base-64 encoded authentication
context (authnCtx) that was passed firstly to your API Gateway and then proxied to your custom
Lambda Function.
For demonstration purposes, you can decode the authentication context using, for example, the BASE64 decoder and encoder or a different online tool. If you need to, for example, modify the context in your Lambda Function or extract information for any purpose, you can decode the authentication context in your Lambda Function. Below, you can find an example of decoded authentication context.