Protecting applications with the use of application metadata
Instructions on how to protect applications using application metadata in ACP
Note
Application metadata can be used for validating policies. It enables, for example, blocking the scope assignment to an application identified with specific metadata.
Prerequisites
- You can log in to ACP as an administrator.
- You have at least one application in ACP.
Configure app metadata
-
Select Applications > Clients from the sidebar.
-
In the client Metadata view, select the Client metadata tab.
-
In the Client metadata view, enter the metadata as a JSON.
-
When your JSON is ready, select SAVE CHANGES.
Result
You’ve configured metadata for the application and you are able to use this data for your purposes.
Create policy
-
Create a Cloudentity policy as described in Creating a policy in the ACP policy editor.
-
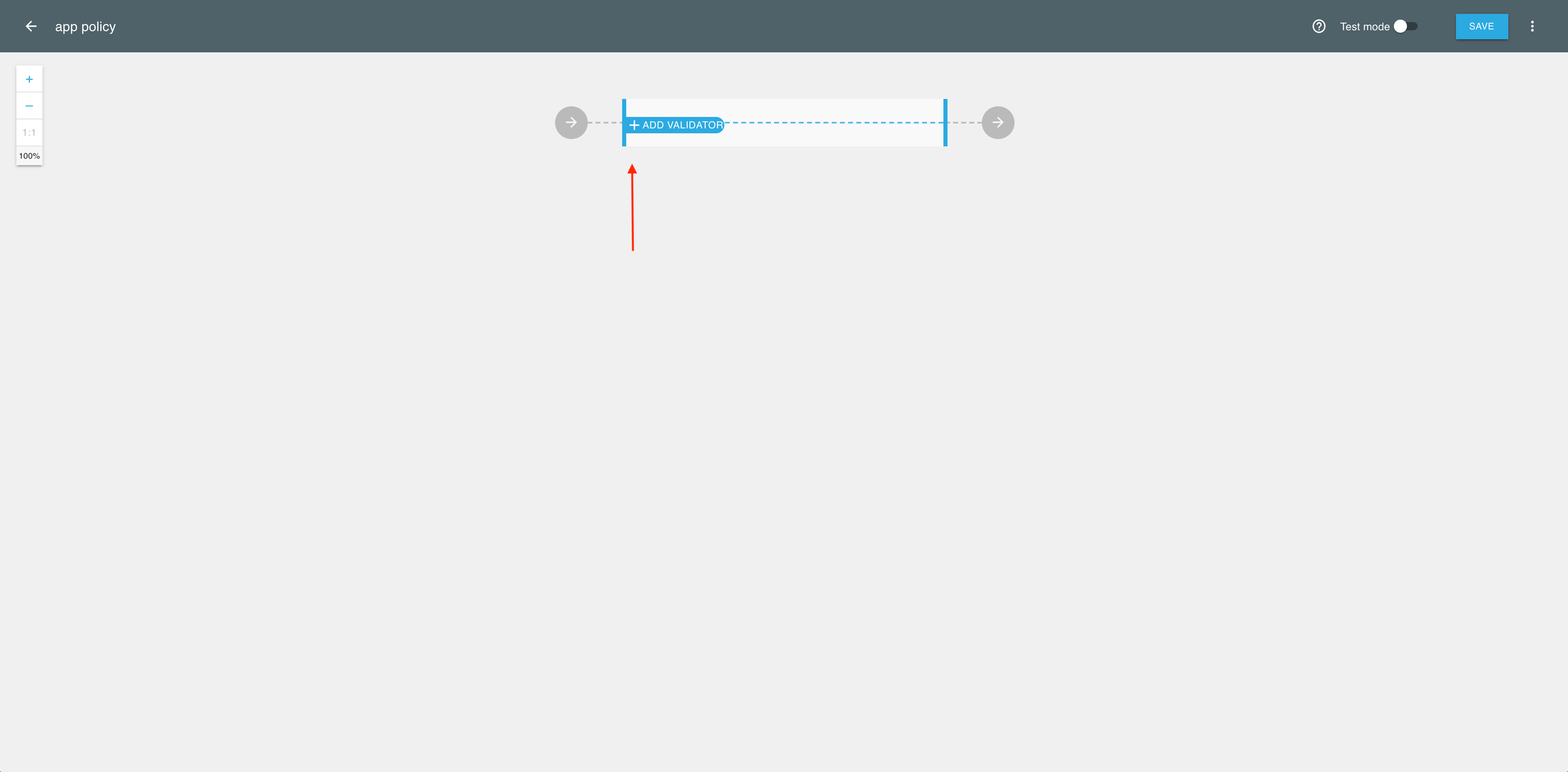
In the policy generating engine, select ADD VALIDATOR.
-
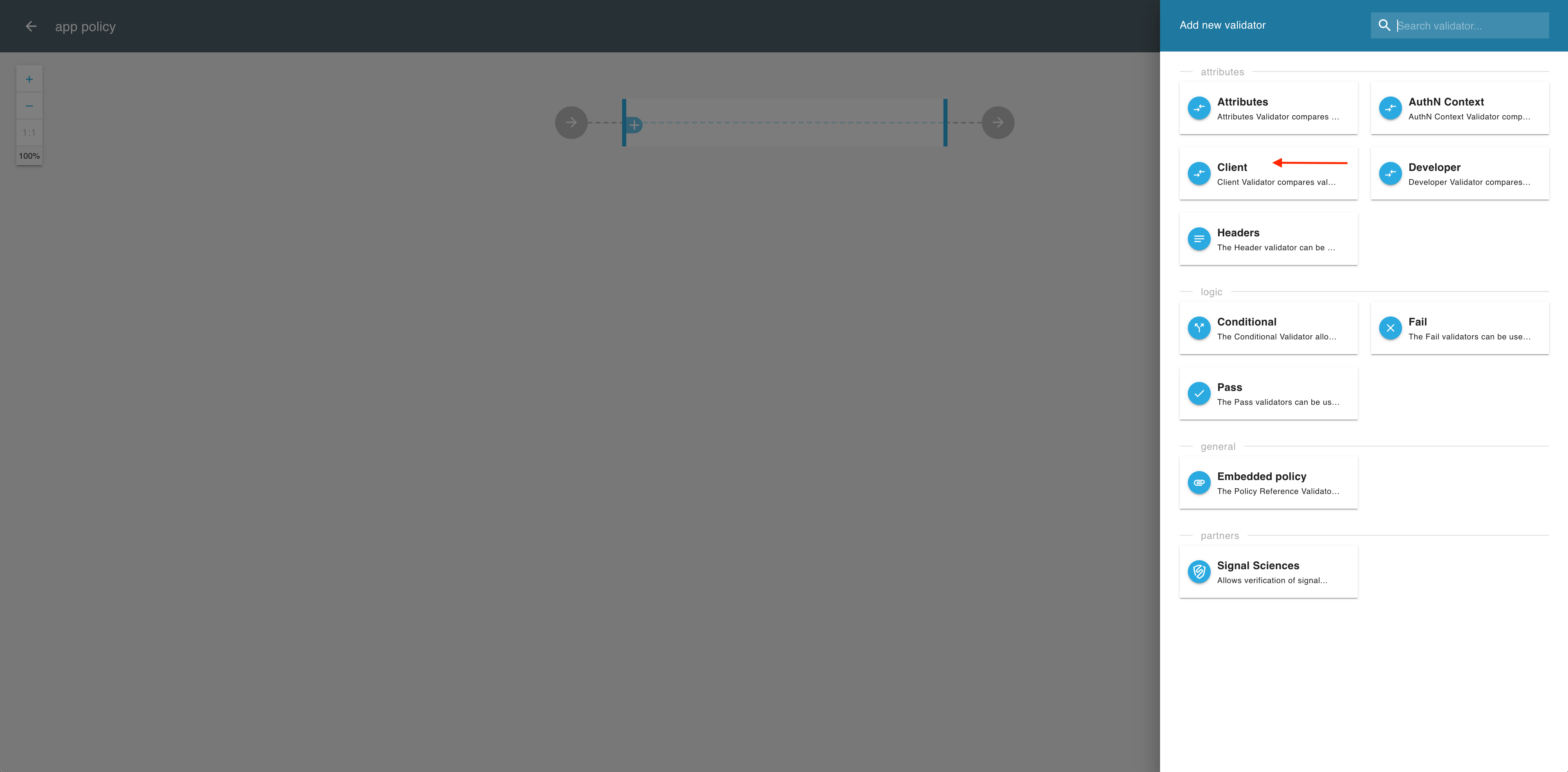
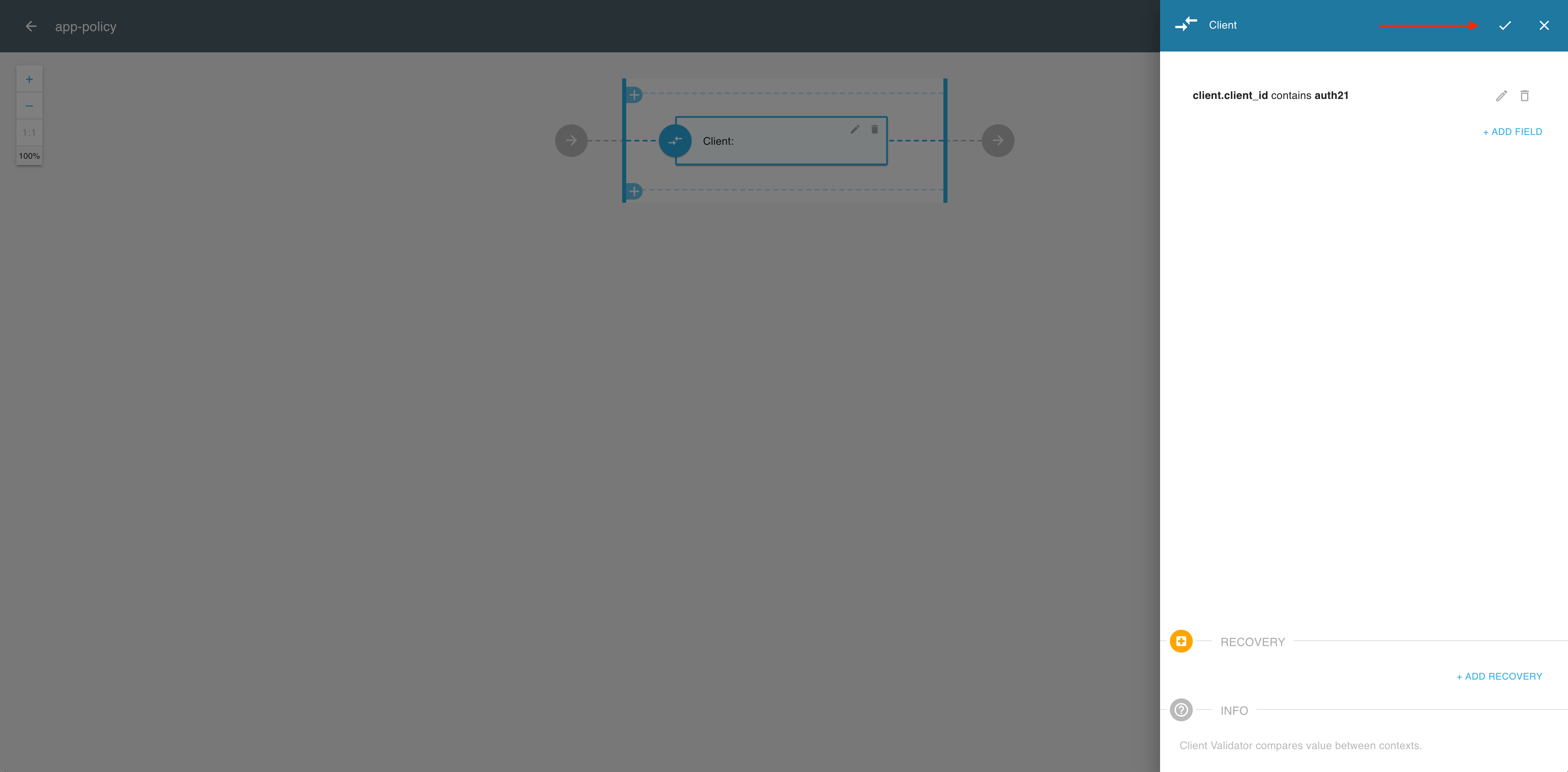
From the fly-out Add new validator pane, select Client.
-
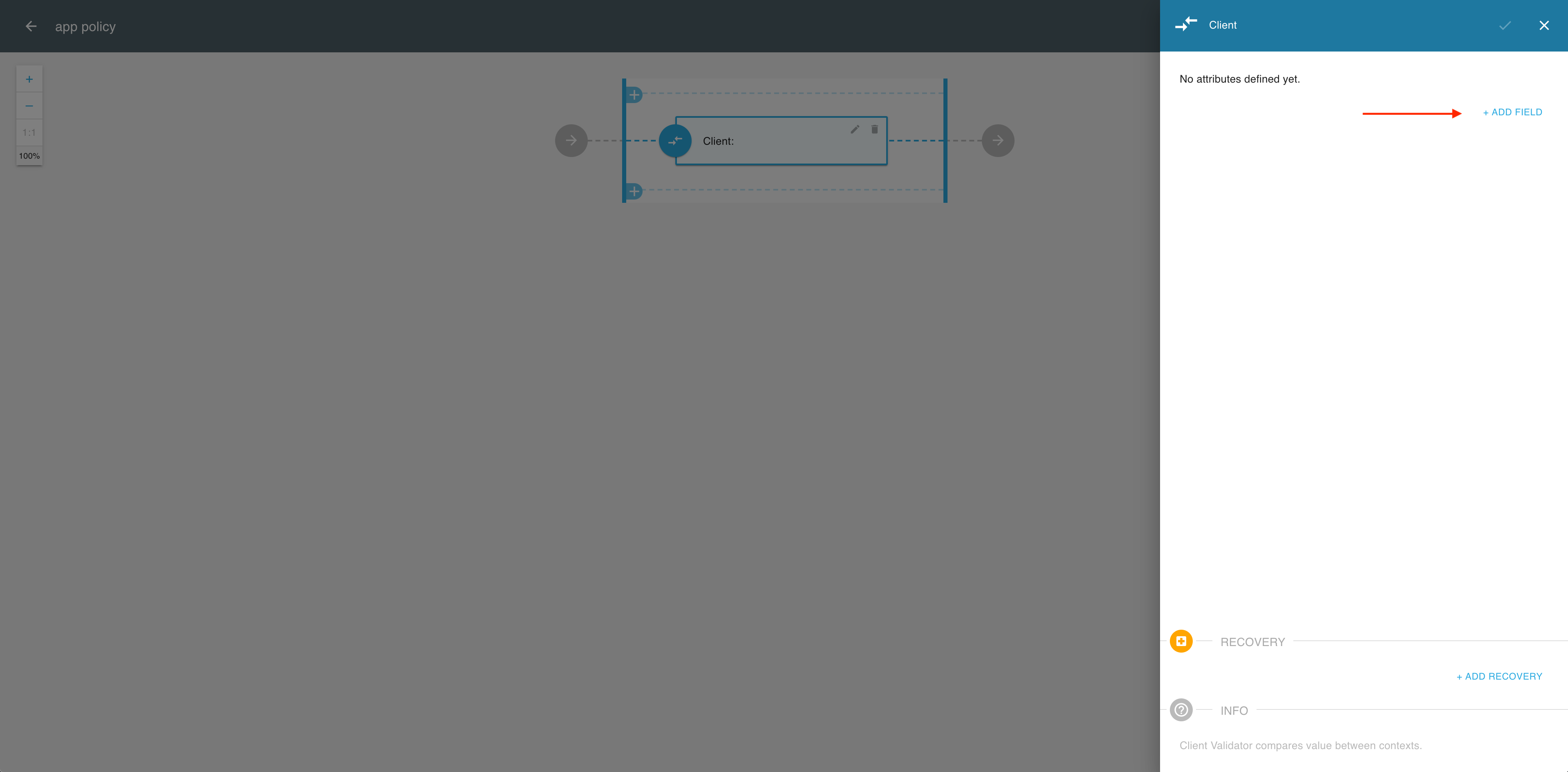
In the Client validator, select ADD FIELD.
-
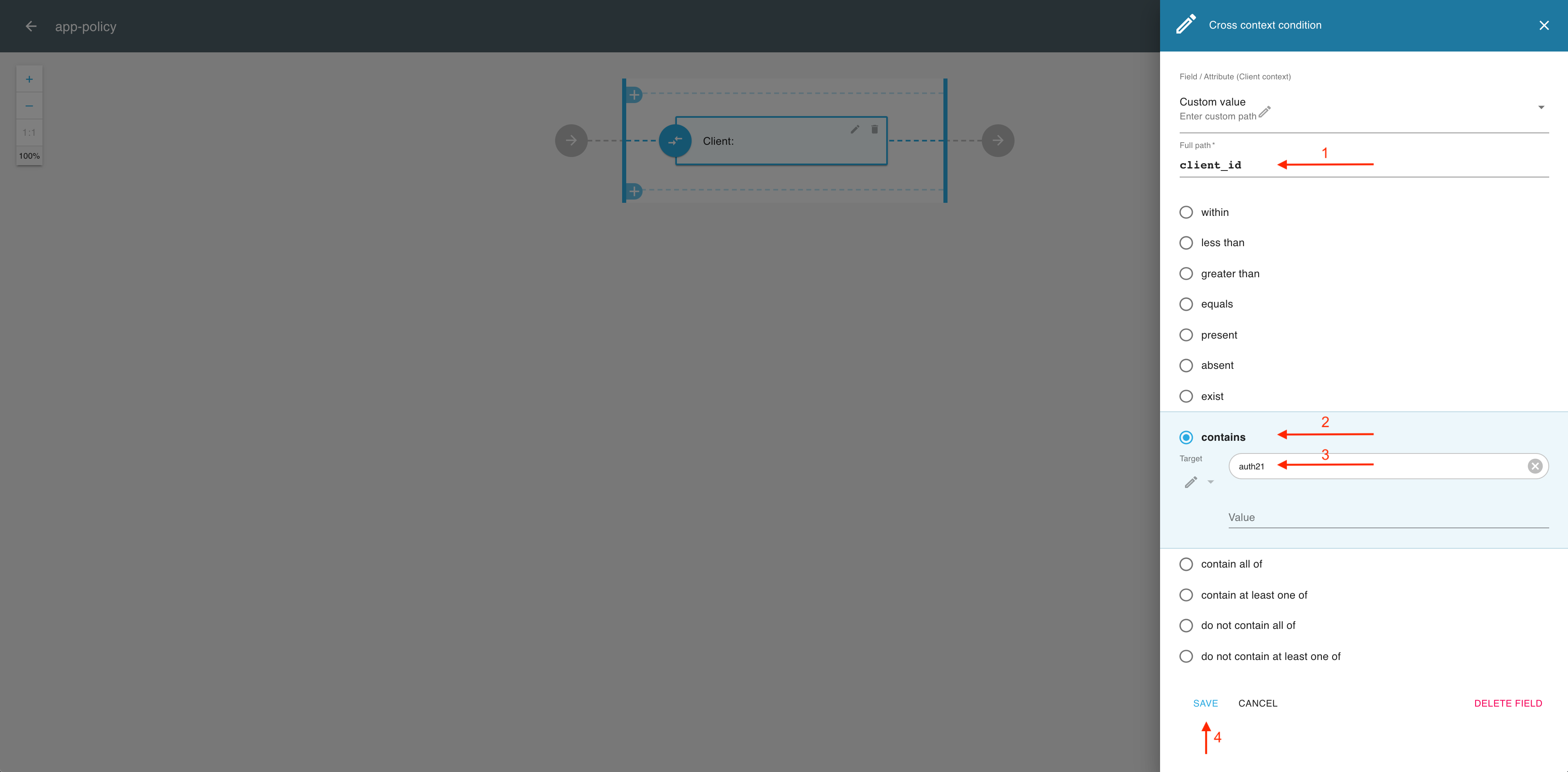
In the Cross context condition editor
- Enter the name of a client-content attribute that you want to use, for example client_id.
- Select an attribute operator, for example, contains.
- Enter a value (target) for your attribute that would validate the policy, for example auth21.
- Select SAVE to complete the field setup.
-
Select the OK icon from the top right corner if you’re done with adding fields.
-
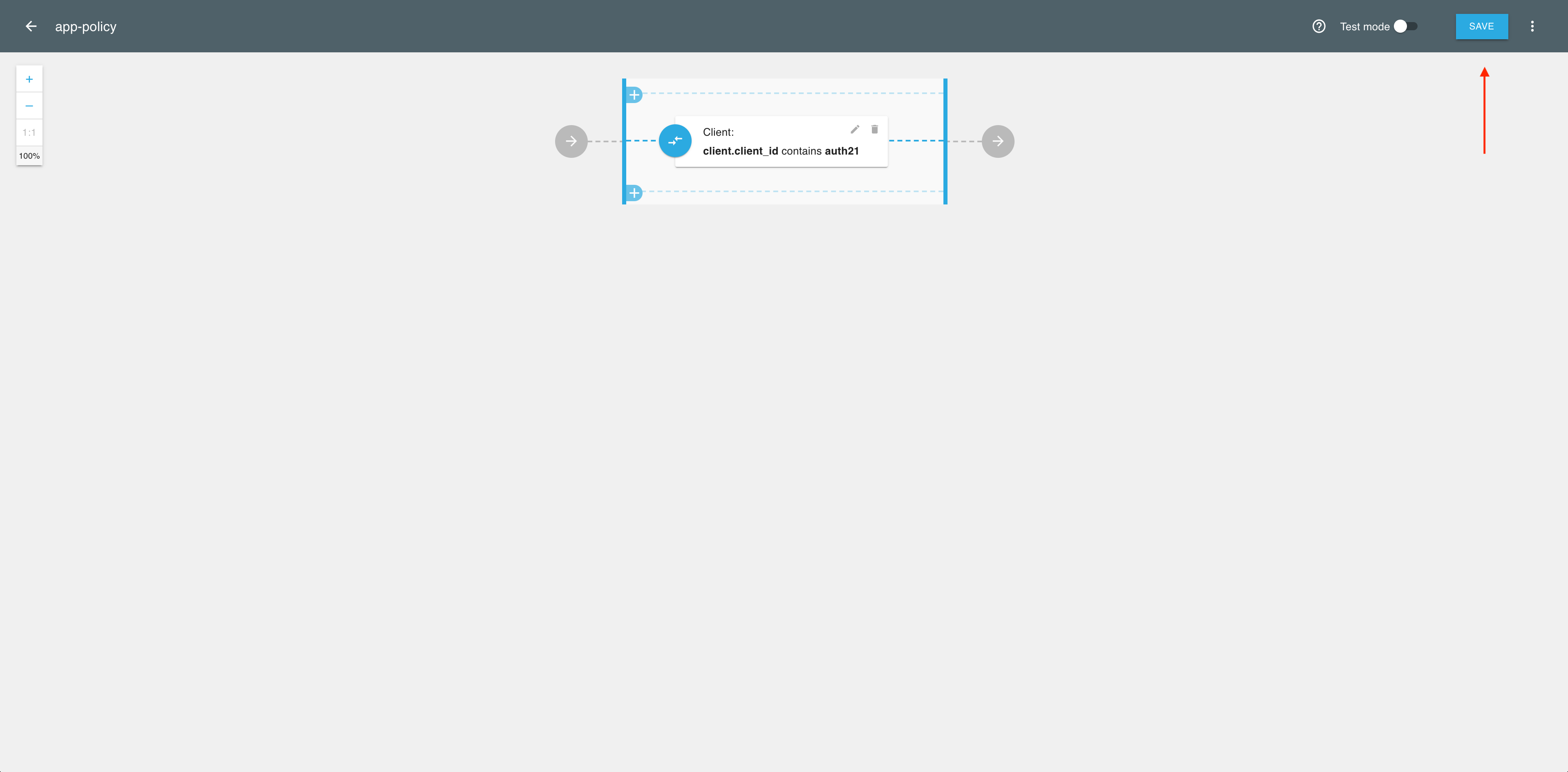
If you’re done with adding validators, select SAVE to complete the policy setup.
Result
Your policy validating application metadata is ready to be used.
Next steps
Use the application metadata for various authorization operations on the 3rd party application in ACP. See, for example, Protecting scopes with access policies as a reference.